Malware for the cyber generation
- Like
- Digg
- Del
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- Yummly
- SMS
- Viber
- Telegram
- Subscribe
- Skype
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Posted: 13 October 2016 | Dr John McCarthy | 1 comment
A word about Cyber Security with Dr John McCarthy. An exclusive blog post from the high-profile Cyber Security Specialist…


I was quite surprised to read the other day a statement by a former FBI Chief.
He said: “We’re not going to solve it (cyber security), folks, not in our lifetime, but we have to constantly manage it.”
He went on to say that we owe it to future generations to manage cyber security effectively or leave a legacy that will make cyber security far easier to manage in the future.
In my opinion we will never solve it
At best we will be locked into an arms race where each side ups their game to get ahead of the other. At the moment the bad guys are way ahead of us and I agree that how we manage cyber security effectively is the best way forward for now and in the future.
Let’s look at some examples in 2016:
Credit card data is being stolen from web sites by using web malware. Then sensitive data is stolen from eCommerce servers. Major vendors and eCommerce systems have been hit.
On the other side of the fence:


Biometric online shopping has arrived. MasterCard has released Identity Check Mobile, a new app that allows cardholders to pay for online purchases using biometrics to authenticate their identity. The app eliminates the need for cardholders to remember passwords or PIN codes. Consumers can use the fingerprint scanner on their smartphone or verify by taking a selfie using facial recognition technology.
“Why would someone do this? Sometimes it’s simply because they can?”
So we see the leap frog of technology solutions and remedies. Each more complex than the last. The new wave of malware that may come along is quite disturbing. Current and emerging new technology involves voice activated “Artificial Intelligence”.
I know that the current devices that serve us by voice control are not true AI but the trend is to develop these super smart digital assistants. As we become more familiar with these and ever more reliant upon them I’m sure malware will play its part and as we come to trust these digital servants they will and do now have access to very personal information. If these systems get infected with malware, then this information is vulnerable to exposure.
“If your plan is for one-year plant rice. If your plan is for ten years’ plant trees. If your plan is for one hundred years educate children.”
Just as likely is the digital servant providing misdirection. This could be done by amending calendar details or as we merge technology into the smart connected car sending us in the wrong direction. Why would someone do this? Sometimes it’s simply because they can. It is appealing to script kiddies and cyber criminals alike.
So how do we manage cyber security for future generations?
As Confucius once said: “If your plan is for one-year plant rice. If your plan is for ten years’ plant trees. If your plan is for one hundred years educate children.”
Training and awareness as always is the key…
About Dr John McCarthy
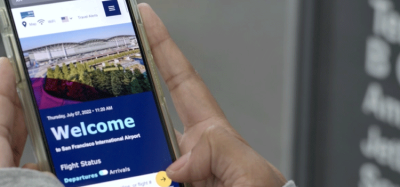
Dr John McCarthy PhD BSc (Hons) MBCS is a renowned authority on cyber security strategy, development and implementation and is an Airport Cyber Security Fellow for ServiceTec Global Services.
Dr McCarthy is frequently invited to sit on expert panels and appear as a speaker at well-known security events including International Airport Review’s own Airport Security and Airport IT events. Past appearances have included talks on ICT Security in the Modern Airport, Security in the Digital Age and SCADA threats in the modern airport.

















Employing a managed IT services provider on a fixed monthly payment plan means that the costs you incur will be predictable and there won’t be any unexpected or hidden charges. This can be very advantageous.