How redundancy concepts ensure maximum system availability in air traffic control
- Like
- Digg
- Del
- Tumblr
- VKontakte
- Buffer
- Love This
- Odnoklassniki
- Meneame
- Blogger
- Amazon
- Yahoo Mail
- Gmail
- AOL
- Newsvine
- HackerNews
- Evernote
- MySpace
- Mail.ru
- Viadeo
- Line
- Comments
- Yummly
- SMS
- Viber
- Telegram
- Subscribe
- Skype
- Facebook Messenger
- Kakao
- LiveJournal
- Yammer
- Edgar
- Fintel
- Mix
- Instapaper
- Copy Link
Posted: 12 February 2020 | Guntermann & Drunck GmbH | No comments yet
Applications in air traffic control are highly sensitive and mission-critical. Therefore, all technical components included in such installations must run reliably.
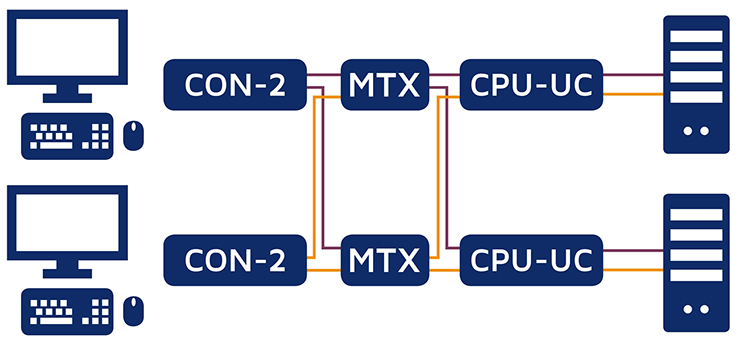
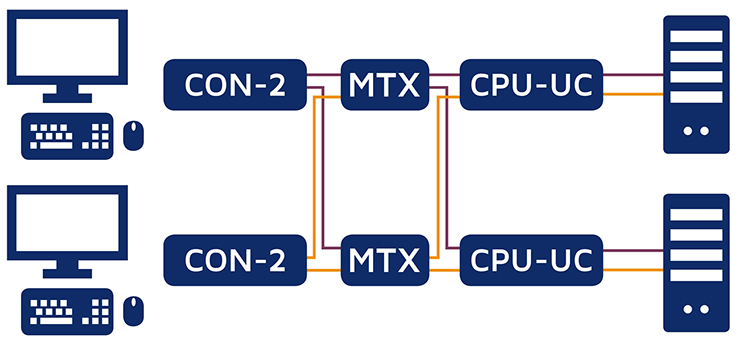
Figure 1: Two-sided application redundancy
KVM systems play an important role when it comes to implementing security concepts and increasing cyber-security. Applying KVM products helps you remove computers from the tower, air traffic control centres, control rooms and all relevant security areas. However, ATCOs can still access these computers remotely – in real time, saving on peripherals, without having to install any software, independent of the operating system. As hardware-based solutions, KVM systems help implement important security concepts, thus minimising the risk of cyber-attacks as the use of software in ATC control rooms increases.
Advantages of applying KVM
Located in a central, air-conditioned server room, computers are protected from any unauthorised access. KVM devices provide a user-friendly basis for uniform operating concepts to harmonise different computer systems, signals, transmission media as well as input and operating devices, thus improving the working conditions for controllers and technicians.
One of the main advantages of using KVM equipment is the simple implementation of security concepts. G&D’s KVM systems can be used to implement a variety of redundancy concepts to significantly increase cyber-security in the tower or ATC centres. Redundant components enable ATCOs to continue their tasks non-stop in their usual working environment, even in the case of failure of an extender line or a system component. Furthermore, redundancy concepts can also avoid a single point of failure.
Comprehensive scenarios for redundant applications
Depending on the security level, some applications require not only redundant computer equipment, but also a redundant operator console and even a completely redundant KVM system. The exemplary application shows an entirely redundant KVM installation. In the event of a failure, a back-up system is available for all computers, matrices and operator stations. Thanks to CPU-UC computer modules and CON-2 console modules, every workstation can access every computer. If a line or module fails, you can automatically switch to the back-up system.
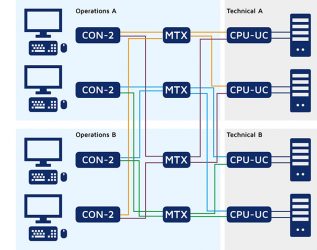
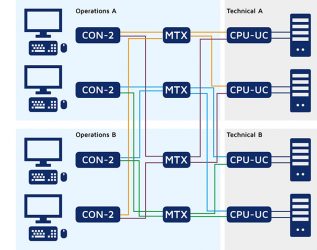
Figure 1 Two-sided application redundancy
Depending on the application’s requirements, even the complex redundant system shown in figure 1 can still be expanded. Highly sensitive, security-critical areas and control rooms go even one step further and require a completely redundantly designed technical area as well as a redundant control room. So what happens if, in the application shown in figure 2, technical room A fails completely due to a fire or another emergency and the KVM matrix and another server in technical room B fail at the same time, for example due to a software bug or a cyber-attack?
In the worst case, one of the two control rooms (in this case control room B) fails completely while one of the two consoles also fails in control room A. Will users still be able to operate their system? Where do they switch to continue with their work?
Thanks to redundant KVM components, systems and premises, employees still have the opportunity to complete their work undisturbed – even in the case of such an extreme scenario. The redundancy concept used for this case shows the maximum level of redundancy. Even if several KVM components, systems and premises fail, the components highlighted in green still allow ATCOs to complete their work undisturbed in their usual environment.
KVM enables numerous redundancy scenarios from simple video contingency to complex and automated switching to backup systems
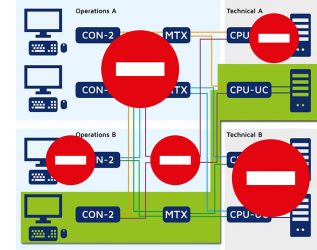
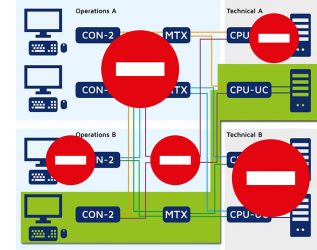
Figure 2: Fully redundant application in Air Traffic Control
In ATC, redundancy concepts are therefore a well-proven option to provide even more security in case of failures. They are complemented by further switching and database concepts, such as the MatrixGuard function for a KVM matrix grid or the syncSwitching function, which guarantees equal switching of redundant matrices.
Expanding redundancies through sync switching of matrices
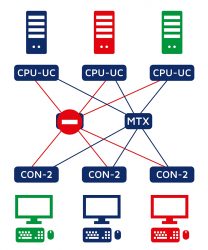
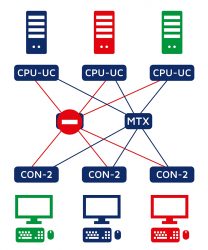
Figure 3: “syncSwitching” guarantees equal switching of redundant matrices
With the ‘syncSwitching’ function, switching states can be synchronised between several redundant, yet otherwise independently operating classic matrix switches. Especially when it comes to redundancy concepts in ATC, it is important to keep the switching states of several matrix switches synchronous. If the primary matrix fails, the system automatically switches to the redundant KVM matrix. The switching states of both matrices are constantly synchronised and automatically apply, thus allowing users to continue their work immediately.
MatrixGuard for even more secure failure scenarios
G&D’s redundancy concepts have proven themselves in numerous ATCs around the world where they increase the reliability and security of complex installations. The various redundancy concepts are supplemented by more switching and database concepts, for example, the MatrixGuard for a KVM grid. A matrix grid enables bidirectional communication between several matrix switches within a network. In this way, systems can be interconnected in an even more complex way to enable larger installations. All matrices are included in the grid work decentrally. However, a defined database master manages the system for the entire matrix grid. In the event of a failure, the matrix grid initially considers the database master a single-point-of-failure, since it supplies the data for the central services. When using the MatrixGuard, each matrix switch within the matrix grid can take over the role of the database master if the original master fails or cannot be reached. This way, all remaining components can still be operated.
Redundantly designed IT infrastructures using KVM bring numerous advantages for air traffic controllers, technicians and the security of applications in ATC. From simple setups with extender lines to complex concepts for fully redundant infrastructures with automatic switching to back-up systems or redundant control rooms – the possibilities for designing redundant structures using KVM systems, and thus increasing application security, are numerous and suitable for every requirement.